… effective cyber deterrence policies require regular, sustained disruption of malicious cyber activity. Such disruption can be technical, legal, logistical, financial, diplomatic, and, in some extreme cases, kinetic. Increasing the scope, scale and tempo of disruption activities should impose high costs on adversaries …
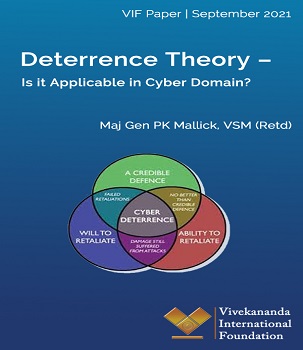
Tags: Cyber attack attribution, Ddeterrence theories, Deterrence in cyberspace, Powers in cyber arena, Principles of cyber deterrence